Most malware in recent days have been intended as tools to steal financial information or other important data. We saw that in the case of Flame and the more recent Gauss malware. Now, security firms have discovered yet another malware which is not as sophisticated but it tries to make your computer unusable. It is being touted as ‘Shamoon.’
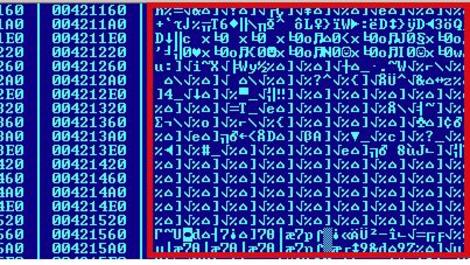
According to Symantec, Shamoon “is a destructive malware that corrupts files on a compromised computer and overwrites the MBR (Master Boot Record) in an effort to render a computer unusable.” It’s rather intriguing for security researchers because most malware authors want to steal information, not to wreck the target machines.
Seculert, another security firm, provided a deeper insight into the workings of this malware. According to the firm, the first stage of the attack involves taking control of an internal machine and then hitching it up to an external Command-And-Control server. Once this is done, this infected machine is used to target other internal machines. In the second stage of the attack, Shamoon malware is released which then steals the data and overwrites MBR (Master Boot Record).
After looking into this new malware, Kaspersky noted, “Our opinion, based on researching several systems attacked by the original Wiper, is that it is not the same. The original ‘Wiper’ was using certain service names (‘RAHD…’) together with specific filenames for its drivers (‘%temp%\~dxxx.tmp’) which do not appear to be present in this malware. Additionally, the original Wiper was using a certain pattern to wipe disks which again is not used by this malware.”
Analysts believe that this malware is more the work of script kiddies who would create such a thing for the sheer fun of it. Any serious attacker wouldn’t want to make the target machine unusable.
Source: SecureList/ Seculert/ Symantec
Courtesy: PC Mag
[ttjad keyword=”cloud-storage-drive”]