Iran has for long decried that a number of cyberattacks have been launched against it by Israel and US but so far, the latter two have always denied having done so. Iranian facilities and computers have been targeted in the past with some of the most sophisticated worms. Now, it has been revealed that U.S. was very actively involved in the whole saga.
New York Times interviewed a number of officials involved in ‘Olympic Games’, the code name for a project that was launched during the days of Bush administration and actually revolved around launching cyber attacks against Iranian nuclear program.
According to the NYT report, one of the most notorious worms we have known to date, Stuxnet, was also actually aimed at Iranian machines but due to a slight programming glitch, the worm entered the web and started infecting systems worldwide.
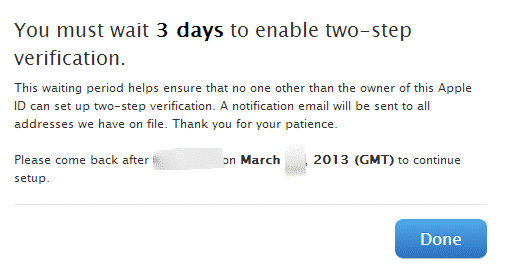
When this leak happened, the Obama administration brought together a high profile meeting where President Obama discussed the possible repercussions of Stuxnet’s leak. However, when he was told that Stuxnet has been able to successfully target and infect Iranian machines, he permitted the project to continue.
Soon after, Iran’s Natanz plant was hit with multiple cyber attacks. One of these attacks was so effective that it was able to take out 1,000 out of 5,000 centrifuges in Iran. So far, US government has been steadily denying any use of cyber weapons. But this NYT report quite squarely shows that US and Israel have been using cyber weapons and cyber attacks to target machines in Iran, a venture that has incidentally wrecked havoc on the entire web more than once.
Recently, another notorious malware, the likes of which haven’t been seen before, has been found by Kaspersky Labs. It has been named ‘Flame’ and it is being suspected that again, US government is behind this malware since a malware of such complexity and functionality can’t be engineered by a hacker or a small group of hackers.
Source: New York Times
[ttjad keyword=”cloud-storage-drive”]

inrnet [url=https://otvetnow.ru]https://otvetnow.ru[/url] independent it consultant