Earlier this week, Cyprus-based security researcher Andrei Costin demonstrated his findings about the weaknesses of air traffic control systems, used globally, at the Black Hat hacking conference in Las Vegas. Costin showed that using $US2000 ($A1930) worth of electronics and a bit of tech skills, hackers could circumvent the air traffic control system. Costin targeted ADS-B system, an air traffic control system deployed internationally in recent years in a multi-billion dollar project.
Costin found that the ADS-B air traffic control system is not designed to verify who is actually sending a message. He mentioned that the position, velocity and other information of a plane which the pilot sends to the air traffic control systems is not even encrypted. So, hackers can breach into the system and send false information about ‘ghost planes’ to the system. The traffic controllers have no way to understand which planes are real and which are not.
Costin explains, “Imagine you inject a million planes; you don’t have that many people to cross-check. You can do a human resource version of a denial of service attack on an airport.” This is like a human version of denial-of-service attacks.
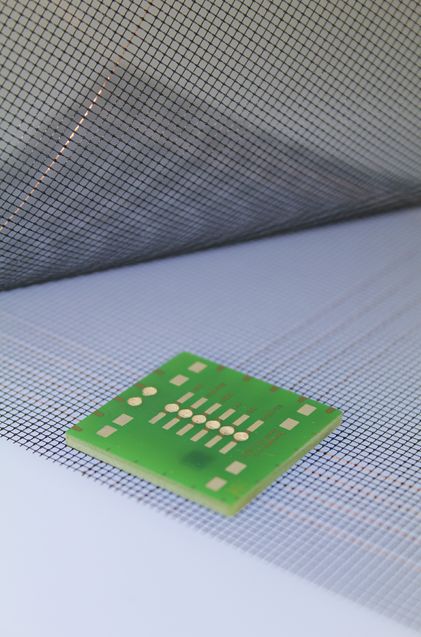
To infiltrate into the system, extract current information of planes and send fake data about planes to the traffic control system, Costin had to use some custom-made electronic devices. The whole thing costed him about $US2000 ($A1930).
The findings are quite alarming. But, that’s not all. Costin also showed how his hardware can collect data of planes on the air, and detect confidential flight information, such as flight path and location of Air Force One (the plane used by US President). He explains, “Basically, you can buy or build yourself a device to capture this information from aeroplanes.”
That means, if the information is used maliciously, that could be deadly.
Source : SBS
Thanks To : Huffington Post
[ttjad keyword=”best-selling-gadget”]