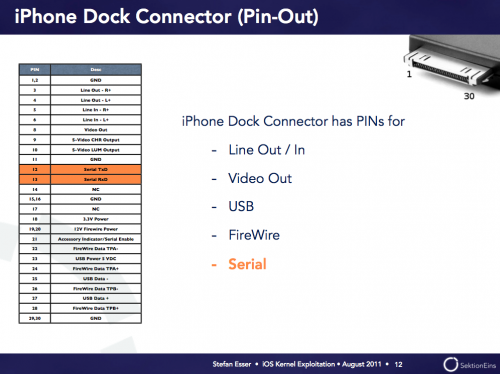
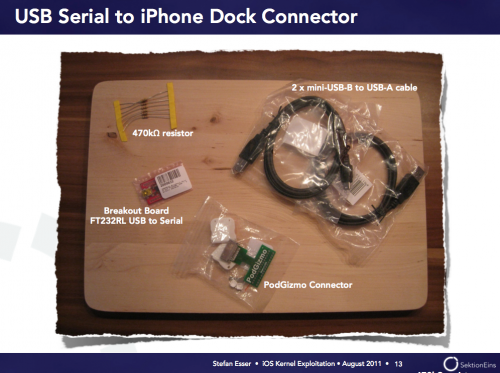
Stefan Esser, also known as I0n1c, the hacker behind the iOS 4.3.1 untether has created an amazing presentation on the latest iOS jailbreak techniques and this is a very technical text with words unknown to most, but contains very interesting information for all fans of jailbreak. i0n1c is the German hacker who first found the exploit to jailbreak iPhone OS 4.2.1 untethered and this exploit was later used to jailbreak iPhone OS 4.3.2 and 4.3.3, but was then corrected by Apple with iPhone OS 4.3.5 and iPhone OS 5. The PDF consists of published technical details sull’overflow, stap on the buffer and heap buffers used to trick the kernel, that acts as a bridge between the hardware and software of the device and you just need for make the kernal is a restistenza to 470kΩ, two mini-USB cable to mini-B USB A connector and a USB adapter to PodGizmo RS232 serial port………………
One of the most active hacker community jailbreak i0n1c, has published 97 pages of text explaining, as he did to make the kernel of IOS to perform the jailbreak of the iPhone and the text quite technical with many words unknown to non working in the sector, but it contains very interesting information for the entire community of the jailbreak. Stefen i0n1c Esser is a security researcher from Germany and he is famous among the jailbreaking community for having found the exploit to jailbreak iOS 4.3.1 untethered. This exploit was used for jailbreaking iOS 4.3.2 and 4.3.3 (JailbreakMe used another exploit), but it was patched by Apple in iOS 4.3.5 and the upcoming iOS 5. The presentation released is 97-pages long and consists of a lot of highly technical details that goes beyond the understanding of your average Joe as i0n1c talks about stack buffer overflows and heap buffer overflows which are used to exploit the kernel and ultimately, how this exploit is used to jailbreak the device. i0n1c used to find the kernel exploits: a 470kΩ resistor, 2 mini-USB-B to USB-A cables, a breakout USB to Serial board and a PodGizmo connector which are connected. If you’re interested in iOS development and have some knowledge of how jailbreaking works, you might want to give i0n1c’s presentation a read. Here is a brief description of what to expect from the entire presentation:
The iPhone user land is locked down very tightly by kernel level protections. Therefore any sophisticated attack has to include a kernel exploit in order to completely compromise the device. Because of this our previous session titled “Targeting the iOS Kernel” already discussed how to reverse the iOS kernel in order to find kernel security vulnerabilities. Exploitation of iOS kernel vulnerabilities has not been discussed yet.
This session will introduce the audience to kernel level exploitation of iPhones. With the help of previously disclosed kernel vulnerabilities the exploitation of uninitialized kernel variables, kernel stack buffer overflows, out of bound writes and kernel heap buffer overflows will be discussed.
Download i0n1c’s iOS Kernel Exploitation Presentation: Here [Direct Link]
[ttjad keyword=”iphone”]


This marks the “End of Apple”
http://bit.ly/dI3hcF