For the last few years, Blackshades has been known as a notorious malware program. The source code of the malware was leaked three years ago but it continues to be sold in underground hacking forums, a Symantec engineer has now revealed.
Blackshades is essentially a remote access tool which is able to take instructions from a command-and-control server once it is inside a victim computer. Through these instructions, it can nick away the usernames and passwords of the user as well as install other nefarious malware on the machine.
Although many people associated with the spread of the malware have been busted in the past, the malware continues to be sold on underground forums. According to Santiago Cortes, a security response engineer at Symantec, the malware continues to infect Windows machines worldwide and hundreds of command-and-control servers are associated with it.
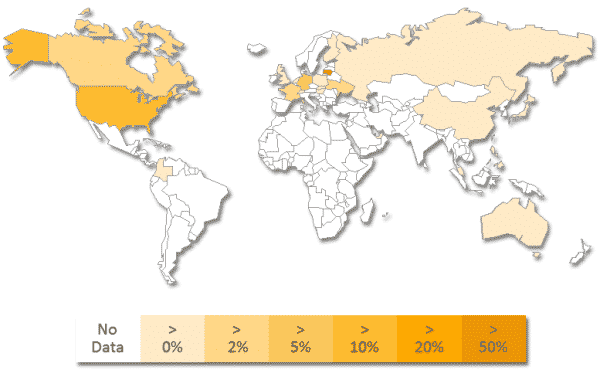
He further reveals that U.S. and Lithuania have the highest number of Blackshades command-and-control servers whereas the majority of Blackshades’ victims are in India, U.S. and U.K. Interestingly, hackers using Blackshades don’t seem to target any select country or community.
Rather, Cortes writes, “The distribution of the threats suggests that the attackers attempted to infect as many computers as possible.” The tricky thing about Blackshades is that it has been modified over time so that it can often avoid detection by antivirus software. Such evolution may explain why the notorious malware continues to be such a popular tool among hackers looking to steal users’ data.
Source: Symantec
Courtesy: PC World
[ttjad keyword=”ipad”]