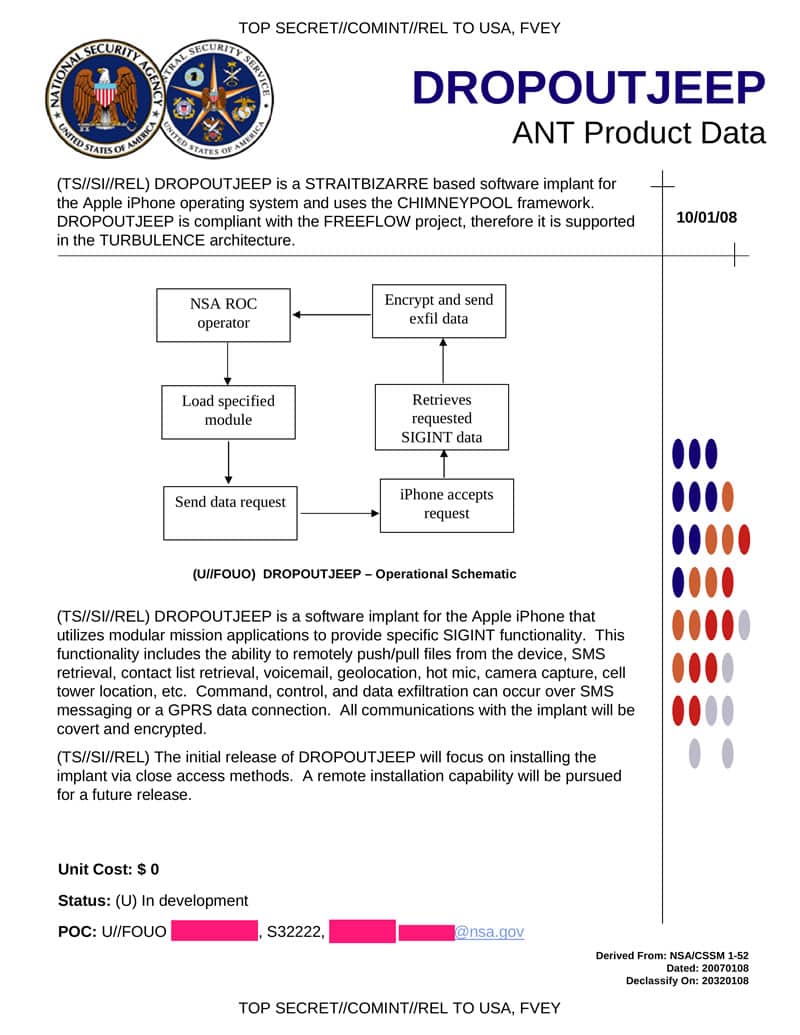
We recently reported how NSA can intercept shipments and bug machines with spyware. Yesterday, an anonymous blogger leaked details of an NSA catalogue, containing backdoor techniques for different hardware tools. The catalogue reveals that the agency can easily access all communications made through an iOS device.
The program that NSA uses to intercept the communications of iOS devices is apparently named ‘DROPOUTJEEP.’ To make this weirdly-named program work, the agency needs physical access to the iOS device it wishes to tap. As soon as it has this physical access, it installs a spyware on the device.
Once the spyware is placed, NSA can read text messages, access contacts list, activate the handset’s microphone and camera and even locate the exact position of the handset. The document from the catalogue containing description of this program claims that it comes with 100% success rate.
What is even more horrifying is that the agency is actively working on a remote spyware version of this program. This would mean that NSA would no longer need physical access to an iOS device to install the spyware – rather, it will be able to do so remotely.
According to Jacob Appelbaum, a security researcher who has been behind some recent revelations about NSA’s operations, “Either [the NSA] have a huge collection of exploits that work against Apple products, meaning they are hoarding information about critical systems that American companies produce, and sabotaging them, or Apple sabotaged it themselves.”
Indeed, it seems improbable that NSA would have access to such a huge stash of iOS exploits, offering the agency up to 100% success rate, without Apple knowing anything about it. But then, we will wait for Apple’s official statement to put things in the clear.
Courtesy: Daily Dot
[ttjad keyword=”android-phone”]