Over the years, an increasingly larger number of states in the U.S. have switched to the online election system. While it is a far more sophisticated, advanced and efficient system, it stands vulnerable to hacking and cyber attacks. And the instance of how bogus absentee ballot requests were sent during Florida elections is just an example of such a happening.
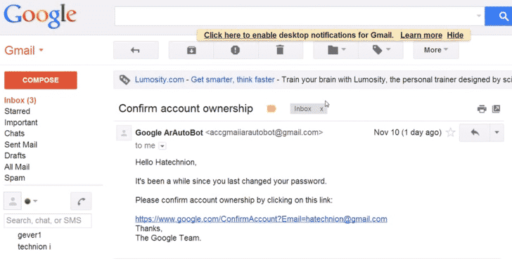
During August, 2012, there was a primary election going on in Miame-Dade County, Florida. During the course of the elections, someone based outside of the U.S. rapidly sent bogus absentee ballot requests to the Department of Elections. A total of 2,500 requests were submitted in an automated fashion, which only means that someone was using a computer program to accomplish this.
The incident marks the first ever cyber attack on the online election system. As to why it is possible and why we haven’t done anything about it, a John Hopkins computer science professor states, “The computer scientists have been saying for many years now that this is going to be possible, and one of the counters to us has been, How come it hasn’t happened? We always say, we don’t know if it’s happened, because it might happen without leaving any evidence. And now we’re finally starting to see proof that it actually does happen.”
However, the problem with Miami’s online ballot request system was that it required no human verification of any sort. Even a simple measure as that could have blocked most of the automated requests.
The voting system used in the Miami-Dade County elections also had a number of other vulnerabilities. And same goes for the online voting systems in many other states. The need is to improve the security of these systems and to put the best experts on them so as to avoid similar cyber attacks and hacks in the future.
Courtesy: CNN
[ttjad keyword=”android-phone”]