With every passing day, new and astonishing PC exploits are discovered. Scientists have, for instance, now revealed that the sounds made by a PC can be used to hack the personal details of its users.
This is a fairly astonishing claim because normally, the sounds made by a PC come from its CPU and are not only complex but also quite low. The exact method involves listening in on the CPU sounds very closely as it encrypts secure information.
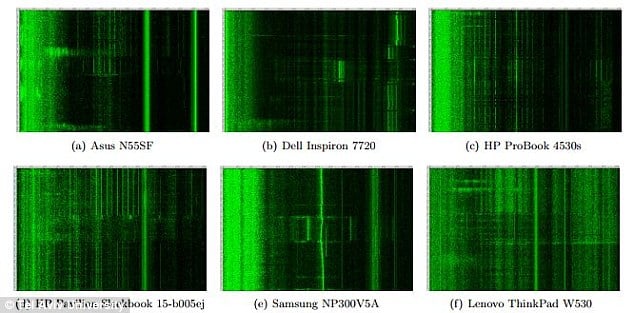
Whenever any information needs to be encrypted using the widely used RSA algorithm, such as when providing login details to a secure site, the CPU makes unique sounds known as loops. Each of these loops correspond to a particular step in the whole encryption and decryption process.
These sounds can be recorded using a mobile microphone. The next part is to take these recorded sounds and match them against unique sounds that correspond to RSA algorithms. Such an analysis of the recorded sounds can reveal the exact RSA key that is used in encryption.
Once a hacker has this information, he can not only access the personal details sent online by a user but may also be able to tap into his login information for online accounts. However, a hacker will need to physically place a low-power microphone near the PC in order to record the sounds. This microphone can be placed within a 13 feet distance of the PC which has to be tapped.
Although there have been no instances where such attacks have been reported to have taken place yet, the researchers say, “We experimentally demonstrate that such attacks can be carried out, using either a plain mobile phone placed next to the computer, or a more sensitive microphone placed 4 meters away.”
Courtesy: Daily Mail
[ttjad keyword=”iphone”]


snowball debt method [url=https://otvetnow.ru]https://otvetnow.ru[/url] picture archive and communication system