When it comes to modern-day digital security, there are so many security loopholes that virtually every other day, a new possible exploit is found by the researchers. At the University of Cambridge, researchers have now discovered a new method which can be used by hackers to steal PIN codes for sensitive smartphone apps.
The method essentially relies on a ‘side channel’ attack, which refers to an attack in which hacker gathers such info from the user’s device which can, in turn, reveal passwords or PIN codes. Ronn Andersen and Laurent Simon of University of Cambridge have now explained how smartphones cameras and microphones can be used to launch such side channel attacks.
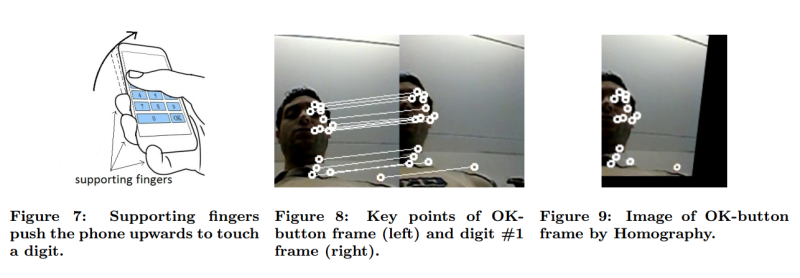
In the paper published on the subject, the duo writes, “By recording audio during PIN input, we can detect touch events. By recording video from the front camera during PIN input, we can retrieve the frames that correspond to touch events. Then we extract orientation changes from the touch-event frames, and we show that it is possible to infer which part of the screen is touched by users.”
In other words, a smartphone’s microphone can be used to record the sounds while you type a PIN code and the camera can be used to guess what parts of the screen you are touching. This method may sound as unreliable but in a test-run comprising of 50 4-digit PINs, this method was able to crack 30% PINs within a few attempts. In five attempts, it was able to correctly identify more than 50% PINs. The researchers encapsulated this PIN-cracking method within a system which they called ‘PIN Skimmer‘.
This shouldn’t be a cause of concern yet because in no instance has any hacker been found of using it. But now that it has been revealed, many will certainly attempt to profit from it. It then remains up to the developers and smartphone vendors to patch up this vulnerability. One way of doing this is to ensure that none of the smartphone sensors are active at all times.
Source: PIN Skimmer research
Courtesy: Giga Om
[ttjad keyword=”kindle”]

debt-consolidation [url=https://otvetnow.ru]https://otvetnow.ru[/url] consolidated debt collection