According to recently published information, the UK Serious Organized Crime Agency is focused on tracking the downloads of files that infringe copyrights with the purpose to find the people behind illegal operations. A couple of days ago, the agency announced as a big success the operation against a website that provided music illegally, RnBXclusive. This website did not provided music files, instead redirected visitors to services similar to MegaUpload.
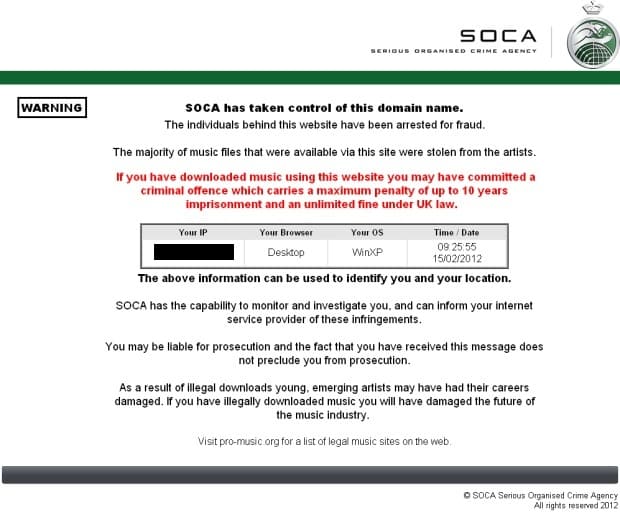
In addition to taking down the website and arresting for fraud the site’s founders and managers, police officers are tracking down the users too. “If you have downloaded music using this website you may have committed a criminal offense which carries a maximum penalty of up to 10 years imprisonment and an unlimited fine under UK law,” warns the message SOCA left on the homepage. Furthermore, the agency informs the site’s visitors that it has the competence to monitor and investigate them and it can inform the service provider of these infringements.
Without hinting to its methods and technology, SOCA’s representatives explained for ZDNet that they can monitor activities of website’s users and it is tracking individual people’s actions.To prove they mean business SOCA’s investigative teams explained in an official statement they have discovered that “a number of site users have deleted their download histories”.
However, despite all the communication strategy meant to discourage people from breaking the laws in the cyberspace, security analysts suggest that SOCA itself might use illegal methods to track down suspects. If SOCA has profs that some RnBXclusive users deleted their download histories, this could mean that the suspects’ computers have been seized and analyzed. If this is not the case, the only other conclusion is that SOCA employs hacking methods. Cybersecurity expert Peter Sommer explained for ZDNet that “If they do that, there is a considerable likelihood that it would be illegal because the law enforcement exemption in the Computer Misuse Act does not apply to the use of a Trojan for remote hacking.”
[ttjad]