This is not new that Federal Bureau of Investigation (FBI) often takes down websites that they want. The latest news is lately, FBI has taken down 27 websites of Tor network.
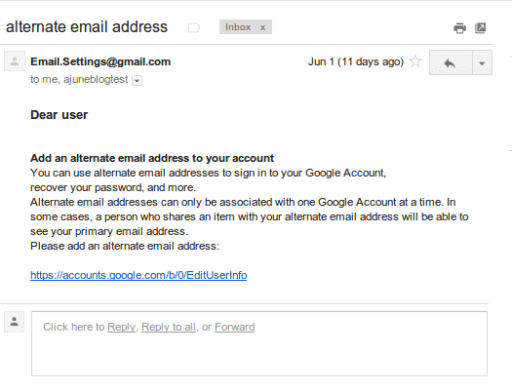
Tor is wildly popular among activists who seek to anonymize their online activities. The browser helps them conceal their online footprints but it is fairly inconvenient to use Tor. A new set of tools collectively called ‘Tortilla’ was devised to make things easier for Tor users. Even users were able to use Facebook by being anonymous.
But the Japanese police ordered the ISPs to block tor. Although some of the ISPs did so, FBI had the complete access to the entire database of TorMail service.
On the other side, Tor network, which is the most common anonymity tool online for hacktivists, activists and yes, cyber criminals too, has lost a significant portion of its credibility over the past few months. And following this, FBI has taken down 27 sites of The Tor Project. Note that The Tor Project is well known for creating the anonymous web browser (the Onion browser) and FBI was after those sites that were surfaced by users via Onion.
FBI has done the shut down operation (code name Onymous) in collaboration with the European Union. Together, they have shut down many hosts and web sites that were offering special services. But FBI hasn’t revealed as to how they discovered Tor’s hidden servers. But FBI has claimed that it has seized 400+ websites and other services.
The very interesting thing is Tor was very much confident regarding its hidden servers. So now it has expressed that it wants to know how FBI was able to find the location of these servers. Tor said that if there was any flaw, then it would be “interested in knowing about it.” But the FBI is not willing to share this secret.
The very surprising things is FBI did not take down jihadi donation site (clone) and also left the real site running on TOR’s server. For those who maintain or use the Tor services can learn from Operation Onymous and help make Tor Project stronger and much more secure.
Source: The Guardian
[ttjad keyword=”security”]