The internet has been abuzz with conversations about the Heartbleed bug for some days now. So what exactly is this bug and how does it affect a user like you? Read the detailed post below to get all the relevant answers.
Heartbleed bug was discovered only a few days ago. It impacted nearly two-thirds of the web, making it one of the biggest online vulnerabilities in the history of the internet. Here’s all the pertinent information about it.
What is Heartbleed?
OpenSSL protocol is considered one of the most secure methods of encrypting vitally important information such as user names, passwords etc. It is used extensively all over the web, by all the major sites, services and networks. Heartbleed is a vulnerability in this OpenSSL protocol. Since the protocol is used by a major portion of the web, the presence of a vulnerability in it directly affects all these users.
Any system that runs the vulnerable version of OpenSSL containing the Heartbleed bug is not secure. A hacker can easily break into such a system with no access rights whatsoever, sneak past all security and gain access to information such as credit card numbers, email addresses, user names and passwords stored on the servers. Not only that, the hacker can nick away this data absolutely undetected, making Heartbleed bug a red-alert level vulnerability.
In essence, the hacker has access to the encryption keys of any given online service, thanks to this bug and he/she can decrypt the traffic from that site, steal information, even impersonate the service in many ways.
What should I do?
If you are a site, an online service or any web-based company that signs up users, the first thing you need to do is update the OpenSSL version that you are using. The updated version of OpenSSL, which effectively patches this bug, is available for server-end deployment.
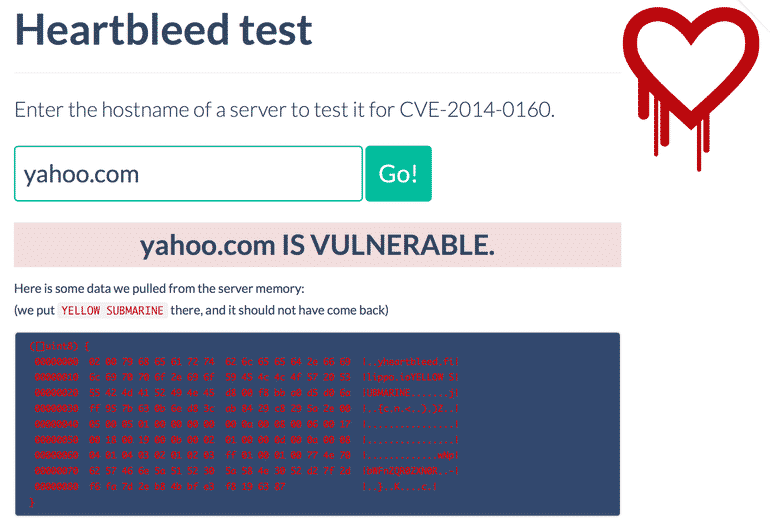
If you are a user, the first thing you need to do is find out the services that are affected by this bug. You can punch in any website here and the Heartbleed test will let you know whether or not it’s compromised. You can further use this Heartbleed hit list compiled by Mashable.
Once you have identified the services and sites that are compromised, it is time to reset your passwords on all of them. For a start, you will need to reset your Gmail, Outlook, Facebook, Twitter and LinkedIn passwords, among others. The password reset will ensure that if anyone accessed your secure login information previously when the Heartbleed bug was around, they can no longer use it since you have a new password now. It is essentially a precautionary measure.
What’s with the name?
Naturally enough, Heartbleed seems more like a term out of a medical book than something that would be used to describe a digital security emergency. The name is derived because this vulnerability is present in OpenSSL’s implementation of a method called ‘heartbeat.’ So appropriately enough, when the method fails and opens a gaping cave of vulnerabilities, Heartbleed seems like an apt name for it.
Courtesy: Heartbleed
[ttjad keyword=”mac”]