If you have been following online hacking attacks by prominent hacking groups, you are probably very well aware of the group named LulzSec. The group is named so because most often, the group tends to launch its hacking attacks merely for the sake of ‘lulz’, which is a reference to thrill and fun. The group had announced during June last year that it was retiring and would no longer carry out hacking operations.
However, since online hacking groups are usually formed of loosely-knitted members, it was inevitable that a splinter group emerged from the now defunct LulzSec. This group called itself LulzSec Reborn.
In fact, we are not even sure that if LulzSec was disbanded at all since a month after its announcement to retire, the group launched an attack on The Sun newspaper. In the past, LulzSec has also been involved in attacking some big-wigs such as AT&T, Sony and U.S. Navy.
It would seem that the hackers from LulzSec have now gathered under the banner of LulzSec Reborn. The group leaked account information of 171,000 military personnel through the website militarysingles.com. And it is back in the news again.
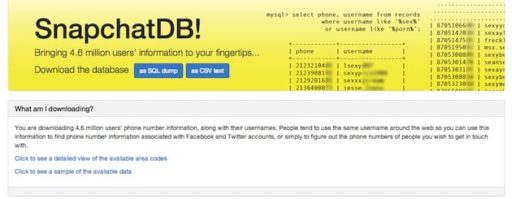
Now, the group has claimed that it was able to hack the account details of 10,000 users of a Twitter-based app called TweetGif. The app required the users to provide all their details including their real names, passwords, locations as well as secret tokens. Somehow, LulzSec claims, it was able to access this information via the app and now the group has made this information public at Pastebin.
Source: Pastebin
Courtesy: Mashable
[ttjad keyword=”cloud-storage-drive”]