The security firm FireEye has spotted a critical vulnerability in Android. The vulnerability allows a seemingly benign app with normal permissions to create fake app icons and route users to malicious sites.
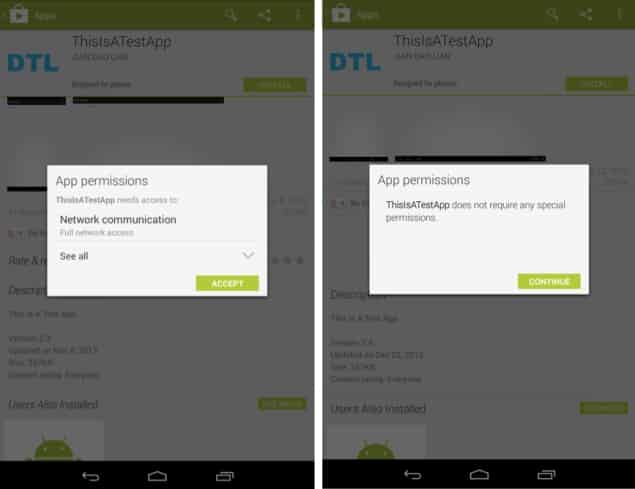
Interestingly, this particular exploit makes use of normal app permissions. Specifically, the permissions called ‘com.android.launcher.permission.READ_SETTINGS‘ and ‘com.android.launcher.permission.WRITE_SETTINGS‘ are exploited by the malware. When granting these permissions, Android typically doesn’t warn the users.
However, with these limited permissions, the malware disguised as an app can wreck havoc on the device. As soon as it is installed, the malware can create fake app icons on the Home Screen. For instance, if you have a banking app’s icon on your Android Home Screen, the malware can replace it with a fake baking app icon.
When you hit the fake icon, you are routed to a malicious site. Such uninformed routing can be leveraged for exploitation in many different ways. The fake site, for instance, can ask you for your financial information and as an unwitting user who is unaware that the site is not authentic, you may end up providing it and jeopardizing your funds.
The worst part is that the Google Play store publishes apps containing this malware without any qualms. FireEye created a proof-of-concept app which exploited the said vulnerability. The app was submitted to the Play store and was accepted into the marketplace. It was later tested on a number of Android devices, including Nexus 7, HTC One and Samsung Galaxy S4, running Android 4.2.2, Android 4.4.2 and Android 4.3 respectively.
In all three, the exploit worked and the permissions used by the malware-ridden app were deemed ‘normal.’ Google has since been alerted about the critical vulnerability and the company has rolled out a patch for it. But it will be some time before all OEM partners apply the patch to their Android devices.
Source: FireEye
Courtesy: Computer World
[ttjad keyword=”android-device”]