Researchers find flaws in Google Chrome OS systems and this flaws could undermine Google’s focus on security of Chrome-powered devices. Google responded to the news of the flaw in rapid fashion and fixed it, but the WhiteHat Security researcher found other instances of the same flaw in other applications soon after. Google Chrome OS gives extensions sweeping rights to access data stored on the cloud and the trusted extensions would be trusting another website, it means Google has to clamp down on extensions………..
Google may see its Chrome operating system as more secure than traditional alternatives, but one security researcher believes the cloud-based OS is vulnerable and Google brags that computers running its recently released Chrome operating system are a lot safer than traditional PCs, partly because user data is stored in the Internet cloud and not on the machine. Yet researchers at an independent computer security firm warn that the Chrome PC’s reliance on Web computing makes it vulnerable to the same attacks that hackers have been launching on websites and Web browsers for years. Matt Johansen, a researcher with WhiteHat Security, said he identified a flaw in a Chrome OS note-taking application that he exploited to take control of a Google email account. He reported it to Google, which fixed the problem and gave him a $1,000 reward for pointing it out. Johansen said he has since discovered other applications with the same security flaw. “This is just the tip of the iceberg,” he told Reuters. “This is just evolving around us. We can see this becoming a whole new field of malware.” Google is betting that the launch of its Web-centric Chrome OS PCs will help reshape the the decades-old personal computer industry, challenging entrenched players such as Microsoft and Apple .
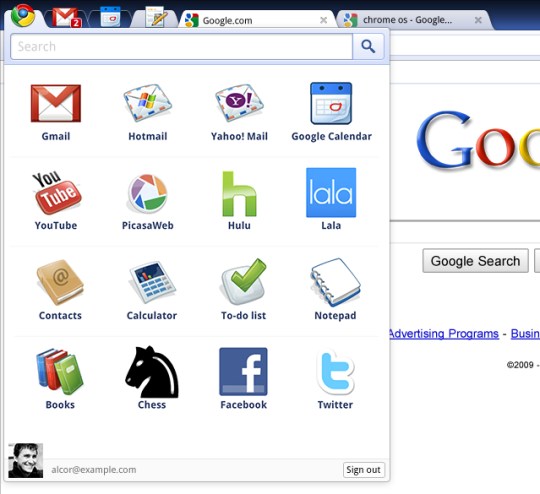
One key to hacking Chrome OS is to capture data as it travels between the Chrome browser and the cloud, Johansen said. Hackers have until now mostly targeted data that sits on a machine’s hard drive. “I can get at your online banking or your FaceBook profile or your email as it is being loaded in the browser,” he said. “If I can exploit some kind of Web application to access that data, then I couldn’t care less what is on the hard drive.” Johansen declined to identify the applications with the security bugs. He and colleague Kyle Osborn are holding back that information for a presentation at Black Hat, a prestigious hacking conference to be held this August in Las Vegas. Those applications belong to a class of software programs known as “extensions,” which users download from the Google Chrome Web Store. Extensions are essentially applications that run inside browsers. The bulk of Chrome OS extensions are written by independent software developers, not by Google. Johansen said the problem with the extensions is related to a design flaw in Google Chrome OS: the operating system gives extensions sweeping rights to access data stored on the cloud. Caesar Sengupta, director of Chrome OS, said the company was exploring “various ways” of trying to automatically tag questionable extensions. Yet he said that Google did not want to make it onerous for developers to get their extensions distributed through the marketplace.
[ttjad keyword=”general”]