The Android Police blog reported on “the mother of all Android malware, discovered in the security system of HTC Android-based devices and the report claims that it is leaking huge amounts of users’ private data. The the flaw has been traced to an application called HTCLoggers.apk, which is in phones with HTC Sense UI package and arange of HTC phones, including EVO 3D and the EVO 4G, now have question marks over the efficacy of their security systems.The flaw is so bad that apparently a user could duplicate the entire phone using information gleaned from the flaw and the flaw was discovered by Trevor Echart and was confirmed by Android Police………………..
Researchers Trevor Eckhart, Artem Russakouskii and Justin Case said the vulnerability affects HTC EVO 3D, EVO 4G, Thunderbolt, EVO Shift 4G, MyTouch 4G Slide, some of the Sensation line and perhaps the upcoming line of Vigor as well as others that are not yet verified and also he created a proof of concept app that requested a single Internet permission yet gained access to cough up almost all the smartphone data. What Trevor found is only the tip of the iceberg, but currently any app on affected devices that requests a single android.permission.INTERNET (which is normal for any app that connects to the web or shows ads) can get its hands on:
- the list of user accounts, including email addresses and sync status for each
- last known network and GPS locations and a limited previous history of locations
- phone numbers from the phone log
- SMS data, including phone numbers and encoded text (not sure yet if it’s possible to decode it, but very likely)
- system logs (both kernel/dmesg and app/logcat), which includes everything your running apps do and is likely to include email addresses, phone numbers, and other private info
Normally, applications get access to only what is allowed by the permissions they request, so when you install a simple, innocent-looking new game from the Market that only asks for the INTERNET permission, you don’t expect it to read your phone log or list of emails. After looking at the huge amount of data that is vulnerable to apps exploiting this vulnerability all day:
- active notifications in the notification bar, including notification text
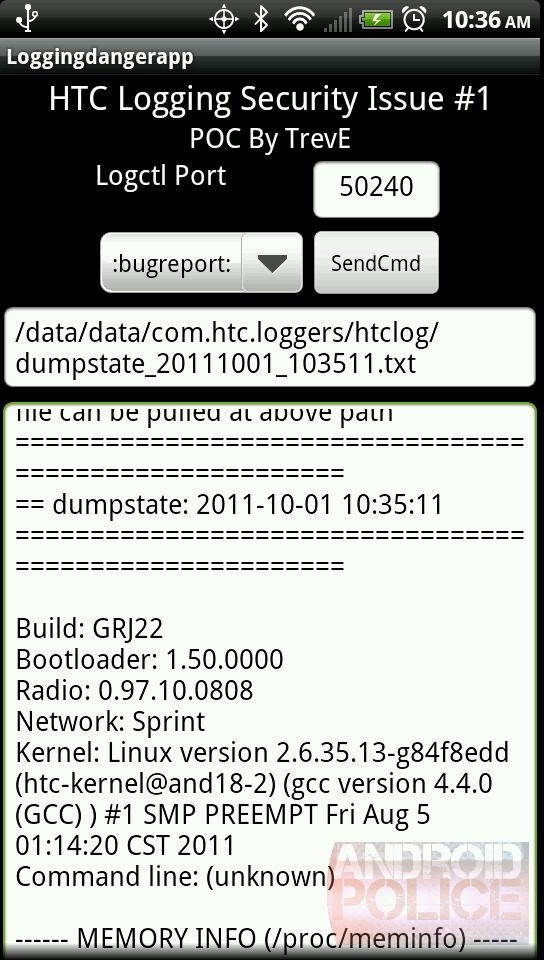
- build number, bootloader version, radio version, kernel version
- network info, including IP addresses
- full memory info
- CPU info
- file system info and free space on each partition
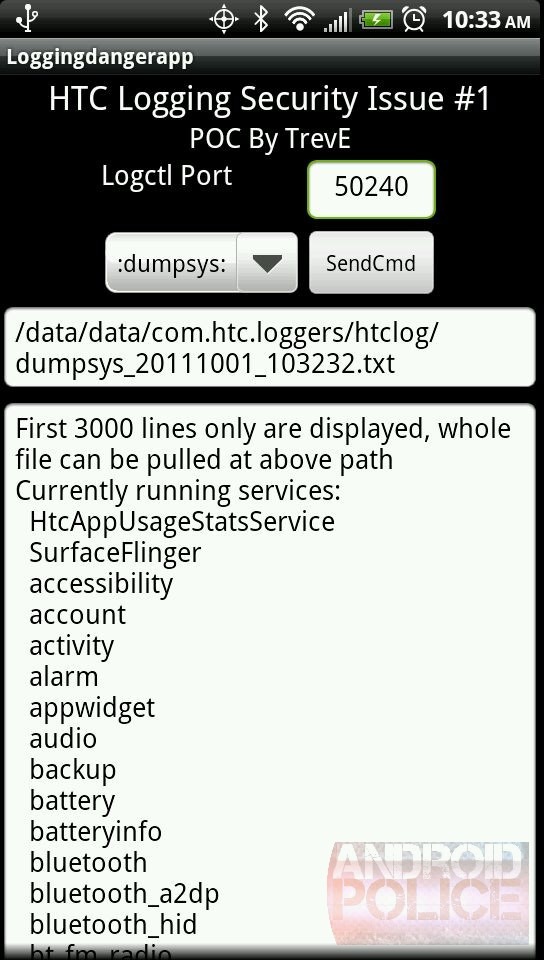
- running processes
- current snapshot/stacktrace of not only every running process but every running thread
- list of installed apps, including permissions used, user ids, versions, and more
- system properties/variables
- currently active broadcast listeners and history of past broadcasts received
- currently active content providers
- battery info and status, including charging/wake lock history
- and more
By using only the INTERNET permission, any app can also gain at leastthe following:
ACCESS_COARSE_LOCATION Allows an application to access coarse (e.g., Cell-ID, WiFi) location
ACCESS_FINE_LOCATION Allows an application to access fine (e.g., GPS) location
ACCESS_LOCATION_EXTRA_COMMANDS Allows an application to access extra location provider commands
ACCESS_WIFI_STATE Allows applications to access information about Wi-Fi networks
BATTERY_STATS Allows an application to collect battery statistics
DUMP Allows an application to retrieve state dump information from system services.
GET_ACCOUNTS Allows access to the list of accounts in the Accounts Service
GET_PACKAGE_SIZE Allows an application to find out the space used by any package.
GET_TASKS Allows an application to get information about the currently or recently running tasks: a thumbnail representation of the tasks, what activities are running in it, etc.
READ_LOGS Allows an application to read the low-level system log files.
READ_SYNC_SETTINGS Allows applications to read the sync settings
READ_SYNC_STATS Allows applications to read the sync stats
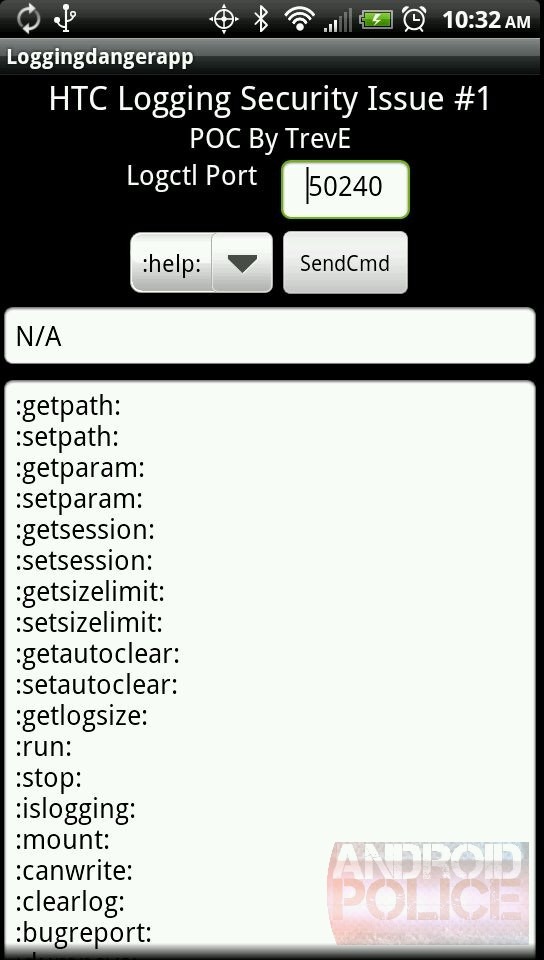
If you’re not familiar with the definition of VNC, it is basically a remote access server. On the EVO 3D, it was present from the start and updated in the latest OTA. The app doesn’t get started by default, but who knows what and who can trigger it and potentially get access to your phone remotely? In addition to Carrier IQ (CIQ) that was planted by HTC/Sprint and prompted all kinds of questions a while ago, HTC also included another app called HtcLoggers.apk. This app is capable of collecting all kinds of data and provide it to anyone who asks for it by opening a local port. Not only just HTC, but anyone who connects to it, which happens to be any app with the INTERNET permission. Ironically, because a given app has the INTERNET permission, it can also send all the data off to a remote server, killing 2 birds with one permission. In fact, HtcLogger has a whole interface which accepts a variety of commands (such as the handy :help: that shows all available commands). Furthermore, it’s worth noting that HtcLogger tries to use root to dump even more data, such as WiMax state and may attempt to run something called htcserviced – at least this code is present in the source:
/system/xbin/su 0 /data/data/com.htc.loggers/bin/htcserviced
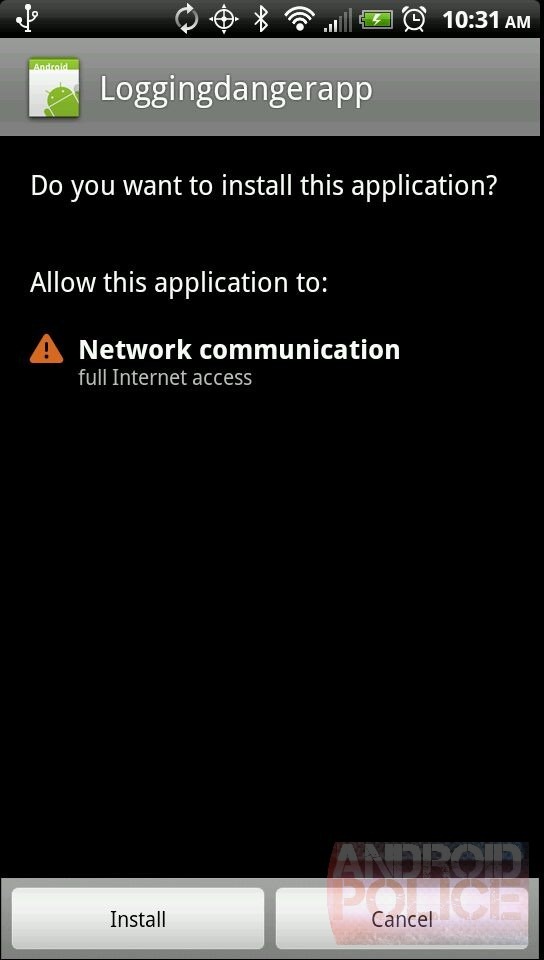
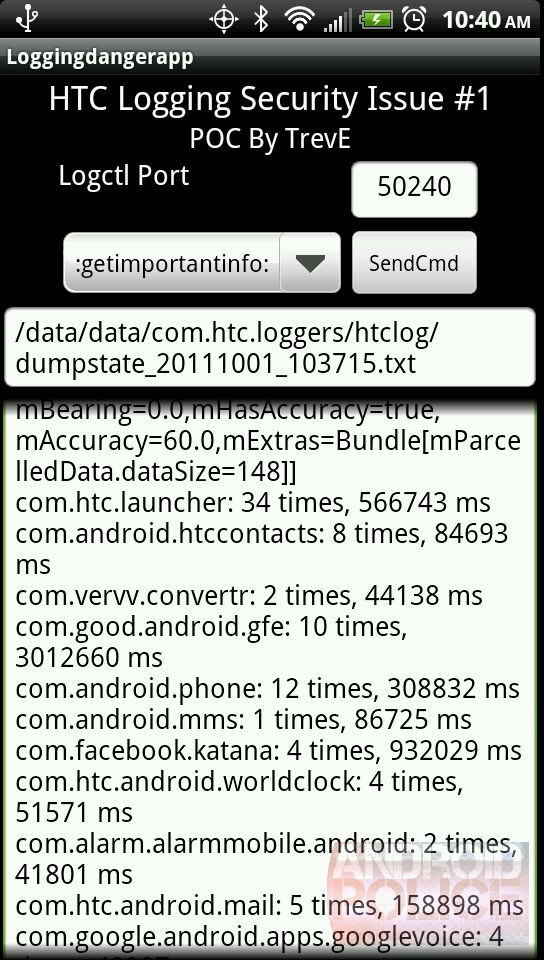
HtcLoggers is only one of the services that is collecting data and in order to help showcase his findings, TrevE created an open-sourced POC (proof of concept) of a simple app that requests a single INTERNET permission, then shows that it can gain access to all the data. There is also a video walkthrough below the screenshots, shot by Trevor himself. Proof of concept source and apk: direct mirror 1, mirror 2.
Affected Phones
Note: Only stock Sense firmware is affected – if you’re running an AOSP-based ROM like CyanogenMod, you are safe.
- EVO 4G
- EVO 3D
- Thunderbolt
- EVO Shift 4G? (thanks, pm)
- MyTouch 4G Slide? (thanks, Michael)
- the upcoming Vigor? (thanks, bjn714)
- some Sensations? (thanks, Nick)
- View 4G? (thanks, Pat)
- the upcoming Kingdom? (thanks, Pat)
- most likely others – we haven’t verified them yet, but you can help us by downloading the proof of concept above and running the APK
HTC’s Response
After finding the vulnerability, Trevor contacted HTC on September 24th and received no real response for five business days, after which he released this information to the public (as per RF full disclosure Policy). HTC is now looking into the issue, but no statement has been issued yet.
[ttjad keyword=”android-phone”]